Lots of people have told you that Linux is cheaper than Microsoft's Windows brand systems; this column explores a different question: what are the risks and consequences of using it at home?
In today's installment I'll look at an issue that's largely unrelated to what you use at the office but is an important determinant of making the Linux at home decision: is it safe for the kids?
The bottom line on having your children use the internet is that you can inoculate them against pornography, whether sexual or violent, but you can't stop them from being curious and you can't stop them from getting to forbidden sites.
| 'twas the winter of 96 |
|---|
|
"Jane" was an input operator for a resume scanning system which used the console
on a Sun workstation along with a SCSI attached scanner. That same machine
acted as the boot host for 18 NCD X-terminals, proxied our internet connection, and
seemed about as sane and reliable as she was, so when she told me that the machine
swore at her and made obscene suggestions, it struck me as a bit odd - especially
since she claimed it had the discretion to do so only when she worked
alone on Saturday mornings.
I came in with her one Saturday to check this out and had just adopted the appropriately condescending expression when the server really did start spouting the most obscene garbage; and loudly too. Worse, this wasn't just obscenities and sound effects, it was stupidly vulgar and violent; kind of a four letter vocabulary play by play on an orgy. So I turned off the speaker and went looking for the cause. That turned out to be the business owner's 13 year old son whose father had developed the habit of parking him in front of one of our 21" NCDs, and firing up IE under Windows 3.11 before going off for a couple of hours. WABI, which we used to run Windows on Jane's workstation, didn't map sound to the remote display, causing "Sunny_1" to seem to swear at her. Personally I was glad the kid was too ignorant to use Netscape in 1600 x 1200 mode with full sound, but I'm still not sure whether to laugh or cry because his response to being caught was to complain about the lack of sound and the size of his (re-sizeable) 600 x 800 window. |
CIPA might be constitutionally valid if the filters were sophisticated enough only to block pornographic material from view by children. However, the evidence adduced during the eight-day trial established that the filters "underblock" by failing to block access to content the libraries want to exclude, and they "overblock" by blocking access to large quantities of material the libraries do not want to exclude. As to the latter, while the libraries seek to exclude sexually explicit material, at times they instead block health and educational constitutionally protected speech on issues such as breast cancer.(Eric Sinrod, in USA TODAY, June 27, 2002)
Obviously meeting your parental responsibilities for teaching your children right from wrong has nothing to do with deciding whether to use Linux or Windows at home - although refusing to buy from people who've been convicted in federal court of anti-competitive behavior is an exemplary moral position the federal government takes in nearly every other case.
On the other hand, choosing Linux can make things a bit easier, or at least cheaper, with respect to a few steps you can take in terms of enforcing your decision not to let them access things like porn or hate sites.
Access logging is probably the single most effective tool you have to enforce your behavioral edicts on your children. After all, if they know that justice, or at least parental disapproval, will be swift and sure, they'll be a lot less likely to offend.
Your challenge, of course, is to get stuff in place they can't turn off or bypass. That's a big problem with a lot of popular blockers and loggers, somebody figures out how to by-pass them and the kids pass the script for that around, thereby making them worse than useless because you'll be the last to find out they've been bypassed.
It should be trivial for someone in one of the open source development efforts for Mozilla, or Konqueror say, to add a patch that would enable you to compile access logging into the browser itself. (The Konqueror log in ~/.kde/share/config/konq_history is easily user deleted, or just replaced with an innocuous list; and running the browser setuid is a recipe for trouble). Having the browser write a log that only root can access would be hard to beat, but it isn't done and I've no idea why not since I got no response when I queried the Konqueror development group.
One effective approach, especially if you're a multi-PC household, is to set up your Linux machine as a proxy server for your home network. That's because a proxy server will handle all external requests - even those coming from a Windows machine using your external connection - and log everything for your review.
| Gudzo! |
|---|
| Capitalizing on the trend to reality television, this wacky weekly comedy features real (but unusually good looking and childless) couples who show us telco or consumer ISP internet services ads and then phone the companies for set-up help with Linux or a Mac. Of course they fill in with "training film" material while on hold... |
The software is free, but getting a proxy server set up is far from trivial, not only because this is intrinsically rather tricky but more importantly because your telco or other ISP is not likely to be excessively helpful. Some, for example, won't assign you a permanent IP address, others won't let you hang your own access device (like a DSL/Router or cable modem with some built in smarts) on the line. That doesn't mean you can't do it, but makes it hard enough that getting it working could become a personal hobby.
Luckily, Linux provides a low tech alternative: just run a software firewall on your Linux machine and ensure that it is the only one that can connect directly to your ISP. This works reasonably well because you can set most firewalls, including several that are free for Linux, to log external accesses but has the downside that it does nothing to prevent them plugging a friend's unprotected laptop into your line.
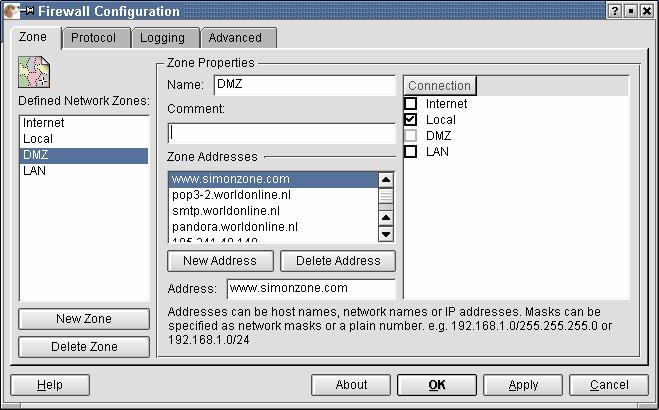
| This screenshot is from the guarddog setup process: |
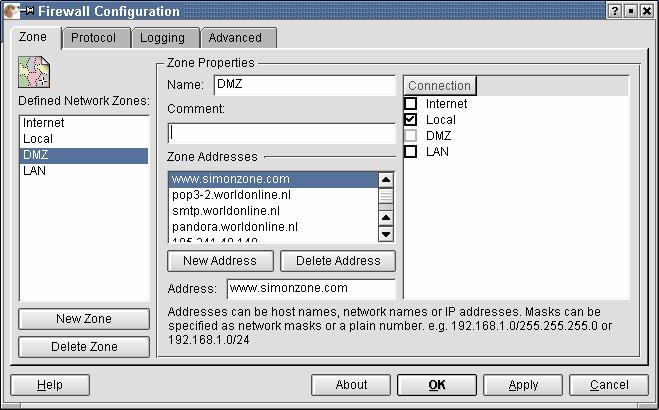
|
You may be thinking, of course, that this recommendation means that you need two or more Linux PCs; after all your office Windows people typically dedicate a machine to each separate task.
Forget it, the Windows rackmount approach to multi-tasking is a solution to a problem - reliability and the complexity of debugging interactions between applications- that simply doesn't exist in the Unix world. Your home Linux machine will cheerfully run multiple concurrent applications with negligible risk of failure, so expect to run the firewall, or your proxy server, on the same machine you use for everything else. That's what we do in big data centers too, where a Windows based design generally calls for lots of mostly idle computers, the Unix guy will usually consolidate until he maxes out the hardware: after all, if you don't have the problem, you don't need to pay for the solution.
next in series (using Linux for learning )